Managing Portfolio Exposure Across L1s, L2s, and DeFi Protocols
Crypto portfolio exposure across L1s, L2s, and DeFi protocols is not a single variable — it is three layers of risk stacked on top of each other, and most investors do not audit even one of them. A portfolio spread across five chains and eight protocols is not diversified. It is fragmented, with compounding vulnerabilities at every layer.
This distinction matters. Cross-chain bridges alone have been exploited for over $2.8 billion — roughly 40% of all value ever hacked in Web3. The risk is not hypothetical. It is structural.
What L1, L2, and DeFi Exposure Actually Means
The terms are used frequently. They are rarely defined with the precision that portfolio management demands.
Layer 1 (L1)
refers to the base blockchain — Ethereum, Bitcoin, Solana, Avalanche. Holding assets on an L1 means exposure to that chain's consensus mechanism, validator economics, and fee structure. If the chain suffers a critical vulnerability or loses developer activity, every asset on it is affected. This is foundational risk. It cannot be hedged within the same chain.
Layer 2 (L2)
refers to scaling solutions built on top of an L1 — Arbitrum, Optimism, Base, zkSync. L2s inherit security from their parent chain but introduce additional risk vectors: bridge contracts that move assets between layers, sequencers that may be centralised, and liquidity that is thinner than on the L1. Ethereum's Dencun upgrade in March 2024 reduced average L2 transaction costs by more than 90%, driving a 10x increase in L2 activity. The capital followed. Base now leads the L2 ecosystem with $4.94 billion in TVL, capturing 43.5% of the analysed L2 market.
DeFi protocols
Aave, Uniswap, Lido, Pendle, GMX — sit on top of both L1s and L2s. Depositing into a protocol adds smart contract risk, governance risk, and composability risk. Composability risk is the least understood: Protocol A depends on Protocol B's oracle, which depends on Protocol C's liquidity pool. One failure cascades.
DeFi TVL surpassed $120 billion by late 2025, with over 60% of that value concentrated in just 12 protocols. That concentration is itself a risk signal. A vulnerability in one of the top five protocols — by TVL — would not be a localised event. It would ripple through every protocol that integrates with it, every L2 where it is deployed, and every portfolio with indirect exposure through derivative tokens or liquidity positions.
The portfolio implication is direct. An investor holding stETH on Arbitrum, deposited into a lending protocol, carries three simultaneous exposures: Ethereum's base layer security, Arbitrum's bridge and sequencer infrastructure, and the lending protocol's smart contract and liquidation logic. These risks compound. They do not cancel each other out.
The Structural Shift: Where Value Accrues Now
The relationship between L1s and L2s has changed materially.
L1 blockchains still capture 90% of crypto market capitalisation. They now collect only 12% of transaction fees — down from 60% in early 2025. Value creation is migrating from base layers to the applications and rollups built on top of them. This is not a temporary trend. It reflects a maturing ecosystem where the settlement layer becomes infrastructure, and the execution layer captures user activity and revenue.
For portfolio construction, this means L1 token holdings and actual value generation are diverging. Holding ETH provides exposure to Ethereum's security premium and monetary properties. It does not automatically capture the economic activity happening on Arbitrum, Base, or Optimism. These are separate allocation decisions with separate risk profiles.
An investor who allocates 100% to ETH and assumes full Ethereum ecosystem exposure is missing this distinction. The DeFi protocols generating the highest fees, the L2s processing the most transactions, and the applications attracting the most users — these represent independent value streams that require independent allocation decisions.
Pantera Capital's approach reflects this reality. Their $1.25 billion fourth fund generated the majority of returns not from base-layer token appreciation but from digital tokens with lock-up periods and special opportunities across the ecosystem — a deliberate multi-layer strategy rather than a single-chain bet.
Case Studies: When Exposure Becomes Loss
The Kelp DAO Exploit — $292 Million (April 2026)
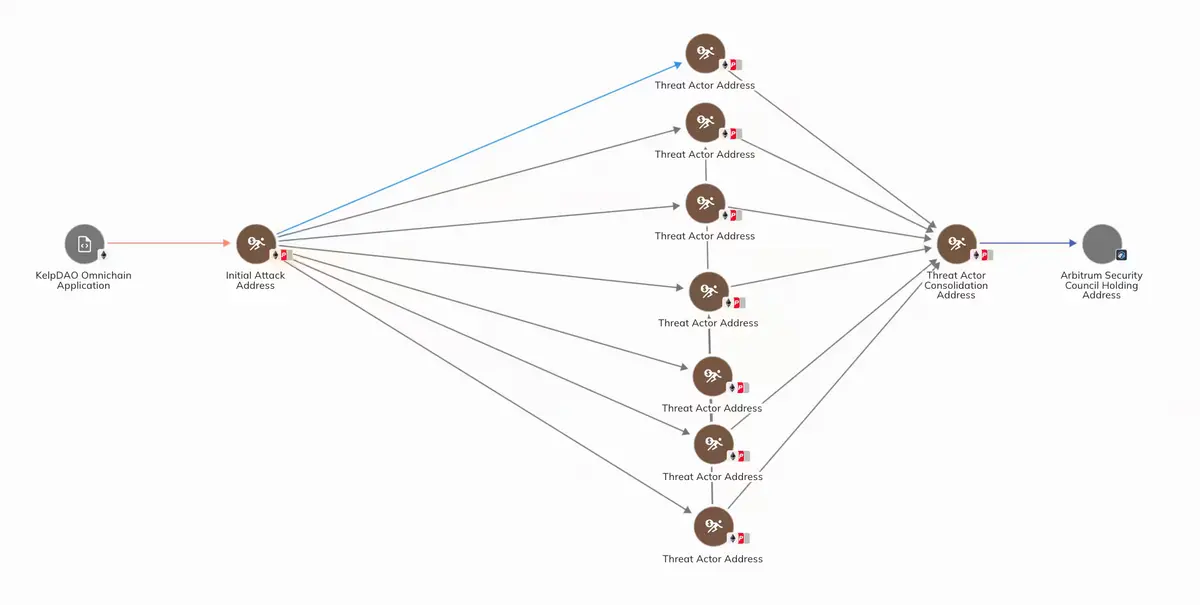
A single misconfigured cross-chain bridge drained $292 million from Kelp DAO. The failure was not in the code itself — it was in the configuration. The stolen assets were immediately deployed as collateral to borrow wrapped ETH, creating a toxic loop of bad collateral backing legitimate debt. The cascade triggered an $8 billion liquidity run across the broader DeFi ecosystem.
The portfolio lesson: bridge exposure is not a secondary risk. For any investor with assets on an L2 or moving between chains, the bridge is a single point of failure. One configuration error erased $292 million and destabilised protocols that had no direct connection to Kelp DAO.
The Ronin Bridge Hack — $600 Million (2022)

The Axie Infinity Ronin Bridge remains the largest bridge exploit in history. Attackers compromised validator keys securing the bridge, draining approximately $600 million. The Ronin chain relied on a small validator set — nine validators, of which five were needed to authorise transactions. The attackers obtained five keys.
The portfolio lesson: sidechain and bridge security is determined by the weakest link in the validator set. A portfolio "diversified" across chains secured by small validator groups carries concentrated, not distributed, risk. The number of chains in a portfolio is irrelevant if those chains share similar security architectures or validator dependencies.
Force Bridge — $3 Million (June 2025)
The Nervos Network's Force Bridge was exploited for over $3 million, with attackers draining USDT, ETH, USDC, DAI, and WBTC. Smaller in scale but instructive in principle: even bridges connecting lesser-known chains carry real, exploitable risk. The assets drained were blue-chip tokens — the bridge, not the underlying asset, was the vulnerability.
The Broader Pattern
These are not isolated incidents. Between 2021 and 2024, bridge exploits accounted for over $2.8 billion in losses. The attack surface — smart contract vulnerabilities, validator compromises, oracle manipulation, configuration errors — is broad and persistent. Cross-chain bridges represent approximately 40% of all value hacked in Web3.
A Framework for Auditing Multi-Chain Exposure
Managing crypto portfolio exposure across L1s, L2s, and DeFi protocols requires a structured audit. The following framework breaks portfolio risk into its constituent layers.
Layer 1: Chain-Level Exposure
Question | What It Reveals |
What percentage of my portfolio depends on Ethereum's security vs. Solana's vs. others? | Single-chain concentration risk |
What is each chain's validator count and decentralisation level? | Base-layer security assumptions |
How much of my portfolio is in chains I could not exit within 24 hours? | Liquidity and lock-up risk |
Layer 2: Infrastructure Exposure
Question | What It Reveals |
How much capital has crossed a bridge to reach its current location? | Bridge exploit exposure |
Does the L2 use a centralised sequencer? | Single point of failure in transaction ordering |
What is the bridge's audit history, insurance coverage, and oracle design? | Infrastructure quality |
Layer 3: Protocol Exposure
Question | What It Reveals |
What percentage of my portfolio is locked in smart contracts vs. held in wallets? | Smart contract risk concentration |
Does any single protocol (e.g., Lido's stETH) appear across multiple positions? | Hidden composability concentration |
What is the real yield vs. token-emission yield of my DeFi positions? | Sustainability of returns |
The Society of Actuaries published a risk classification framework that organises DeFi vulnerabilities into three layers: technical/code, economic/protocol, and infrastructure/cross-chain. This taxonomy maps directly to the L1-L2-DeFi exposure stack. An investor who audits only one layer is auditing a third of the risk.
Allocation Models for Multi-Chain Portfolios
Institutional frameworks have converged on a core-satellite structure for multi-chain portfolio management. The following table adapts the XBTO and 21Shares models for portfolios with cross-chain DeFi exposure.
Allocation Tier | Conservative | Balanced | Aggressive |
Core (BTC + ETH) | 80% | 65% | 50% |
L1/L2 Ecosystem (SOL, ARB, OP, BASE tokens) | 10% | 20% | 25% |
DeFi Thematic (RWA, AI-DeFi, Restaking) | 5% | 10% | 15% |
Stablecoin Reserve | 5% | 5% | 5% |
Speculative (Airdrops, Early-Stage) | 0% | 0% | 5% |
Rebalancing Frequency | Quarterly | Quarterly | Monthly |
Drift Tolerance | ±8% | ±10% | ±10% |
Three principles underpin these models.
Principle 1: Chain diversification is not token diversification. Holding five tokens on Ethereum is single-chain exposure. Holding ETH, SOL, and AVAX is chain diversification — exposure to three independent security models.
Principle 2: Bridge exposure deserves its own line item. Any asset that has crossed a bridge carries residual bridge risk even after it arrives on the destination chain. The audit framework above treats this as a separate risk category, not a footnote.
Principle 3: Liquidity fragmentation is a cost, not just a risk. Academic research analysing Uniswap v3 across Ethereum and its rollups found that 66% of Ethereum's liquidity is suboptimally allocated — liquidity providers would earn higher returns by reallocating to L2s. For portfolio managers, this means the chain where an asset is held affects not just security but also execution quality, slippage, and yield.
Nansen's multi-chain tracking platform operationalises these principles through real-time PnL tracking, risk scores, and Smart Money attribution across chains and protocols. The tool does not eliminate the risk. It makes it visible — which, for portfolio management, is the first requirement.
What This Means for Managed Portfolio Investors
Not every investor wants to audit bridge configurations and sequencer architectures. Nor should they need to.
Managed crypto portfolio strategies — including those offered by platforms like Grade Capital — abstract away multi-chain complexity. The fund manager handles chain selection, bridge risk assessment, protocol due diligence, and rebalancing. The investor holds a single position denominated in a stable unit (typically USDT), with professional risk management across the underlying layers.
This is the same logic that separates index fund investors from stock pickers in traditional finance. The underlying complexity does not disappear. The management of it transfers to a professional with the tools, data, and mandate to handle it continuously.
The Cost of Not Auditing
The numbers are not abstract. $2.8 billion in bridge exploits. $292 million from a single configuration error. $600 million from five compromised validator keys. $8 billion in secondary liquidity contagion from one protocol's failure.
A portfolio spread across multiple chains and protocols without a structured exposure audit is not diversified. It is exposed — in ways the investor may not see until a loss event makes them visible.
The frameworks exist. The data exists. The tools exist. The question is whether the audit happens before or after the loss.
Multi-chain portfolios are here to stay. So are the risks embedded within them. The difference between a diversified portfolio and a fragmented one is not the number of chains or protocols — it is whether the investor understands the exposure each layer carries and has a plan for managing it.
Past performance is not indicative of future results. This content is for informational and educational purposes only and does not constitute financial advice or an offer to invest.